Pentagram Secure Services
- Home
- Services
We Build Secure Systems
Our Penetration Testing Capabilities

External Network Pen-Testing
Using state-of-the-art software scanning tools and manual techniques, our external security assessment looks for areas that may be exposed to malicious attacks through your firewall or through social engineering.

Internal Network Pen-Testing
Evaluate the quality of your internal network technical control by performing a deep scan of all internal IP addresses. Our internal security also assessment prioritizes potential vulnerabilities.

Wireless Pen-Testing
Wireless penetration testing is a method of identifying and exploiting security weaknesses in Wi-Fi networks. It is an essential measure for organizations that depend on wireless networks for their operations.
Mobile Pen-Testing
Mobile Penetration Testing is the process of identifying and exploiting vulnerabilities in mobile applications. The method may include decompiling the application to identify any defects that could lead to bugs.

External Network Pen-Testing
Using state-of-the-art software scanning tools and manual techniques, our external security assessment looks for areas that may be exposed to malicious attacks through your firewall or through social engineering.

Internal Network Pen-Testing
Evaluate the quality of your internal network technical control by performing a deep scan of all internal IP addresses. Our internal security also assessment prioritizes potential vulnerabilities.

Wireless Pen-Testing
Wireless penetration testing is a method of identifying and exploiting security weaknesses in Wi-Fi networks. It is an essential measure for organizations that depend on wireless networks for their operations.
Mobile Pen-Testing
Mobile Penetration Testing is the process of identifying and exploiting vulnerabilities in mobile applications. The method may include decompiling the application to identify any defects that could lead to bugs.

Social Engineering
Social engineering penetration testing mimics techniques such as phishing and pretexting to identify human weaknesses and reduce the risk of information leaks, unauthorized access, and fraud.

Social Engineering
Social engineering penetration testing mimics techniques such as phishing and pretexting to identify human weaknesses and reduce the risk of information leaks, unauthorized access, and fraud.

PCI Card Vulnerability Assessments
PCI card vulnerability assessments are essential for organizations that handle cardholder data to ensure compliance with PCI DSS. These assessments involve a systematic process to identify and address vulnerabilities in systems handling cardholder data, such as weak firewalls, outdated software, or open ports.

Firewall rules review
A firewall configuration review involves performing a detailed manual review of your firewall configuration, looking for deviations from security best practices and potential security vulnerabilities.

Office 365 Azure Security Architecture Review
Perform a security best practices review of your Azure/O365 environments with prioritized recommendations for hardening.

VPN Assessment
VPN AssessmentVPN penetration testing is a critical practice for ensuring the security of Virtual Private Networks. It involves simulating cyber attacks to identify vulnerabilities that could be exploited by malicious actors. This process helps organizations proactively address security weaknesses before they can be exploited in real-world attacks. The testing typically includes planning, port scanning, #ngerprinting, and exploiting vulnerabilities to assess the e$ectiveness of existing security controls. It is essential for compliance with data security and privacy regulations, demonstrating a commitment to robust cybersecurity practices, and building trust with clients and stakeholders
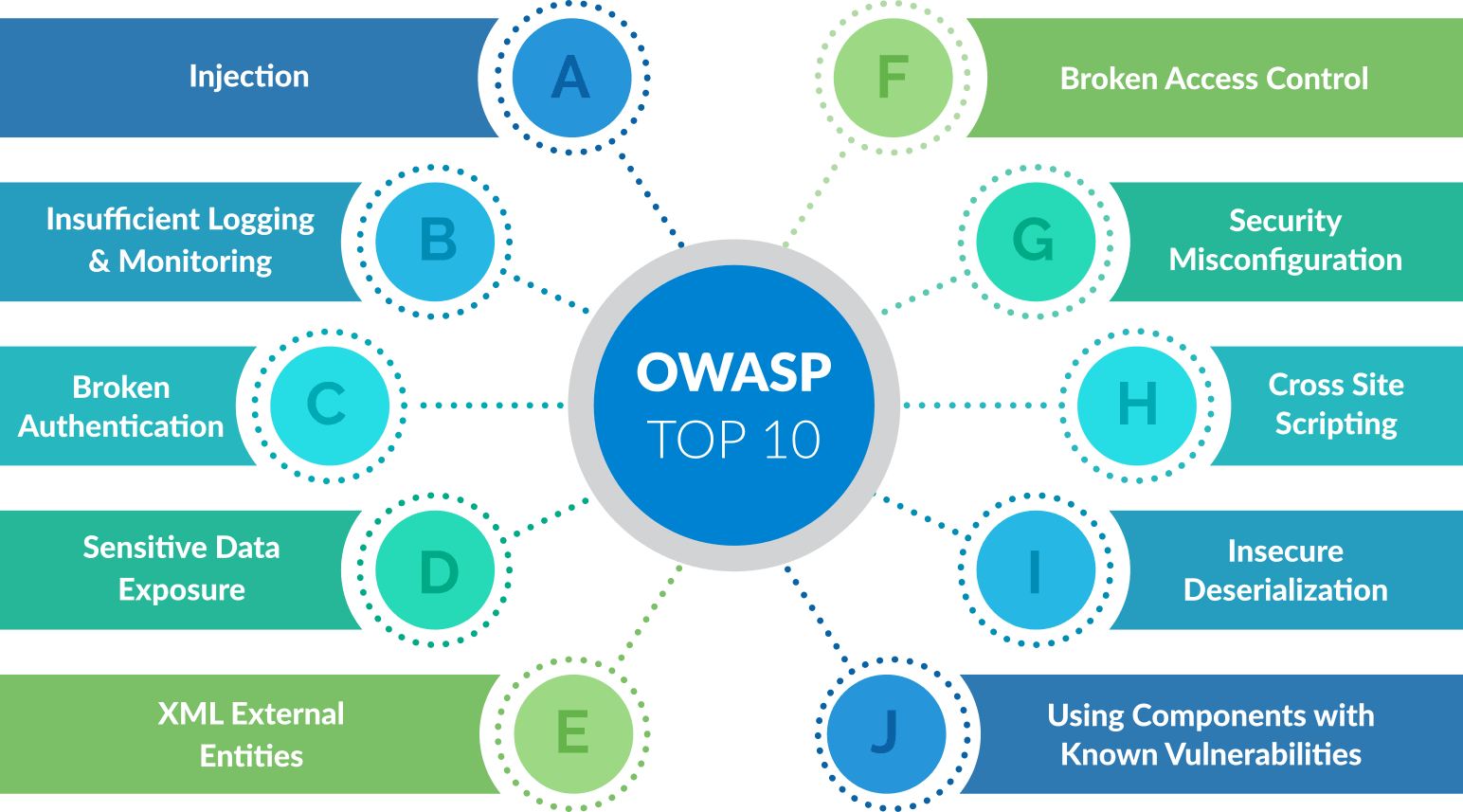
Web Application Penetration Testing (OWASP 10)
OWASP web application penetration testing is a security assessment methodology focused on identifying and validating the most critical security risks de#ned by the Open Worldwide Application Security Project (OWASP). At Pentagram Secure, our testers utilize the OWASP Top 10 as a primary framework to ensure coverage of high-impact vulnerabilities.

Active Directory Penetration Testing
Active Directory (AD) penetration testing simulates real-world attacks to #nd weaknesses in an organization's AD infrastructure, focusing on gaining unauthorized access, escalating privileges, moving laterally across the network, and ex#ltrating data by exploiting miscon#gurations, weak credentials, and vulnerabilities in user/group policies, ultimately helping secure critical identity and resource management. At Pentagram Secure, our testers use techniques like credential theft, NTLM/Kerberos relay attacks, and enumeration to uncover 4aws, mimicking attackers' steps to provide actionable remediation advice

Digital Forensics
Digital forensics, also known as digital forensic science, encompasses the recovery and investigation of material found in digital devices, often in relation to cybercrime. It has evolved from its origins in computer forensics to include all devices capable of storing digital data, such as computers, smartphones, tablets, and IoT devices. At Pentagram Secure, our forensic examiner primary goal is to preserve evidence in its original form while conducting a structured investigation, which is crucial for legal proceedings.

PCI Card Vulnerability Assessments
PCI card vulnerability assessments are essential for organizations that handle cardholder data to ensure compliance with PCI DSS. These assessments involve a systematic process to identify and address vulnerabilities in systems handling cardholder data, such as weak firewalls, outdated software, or open ports.

Firewall rules review
A firewall configuration review involves performing a detailed manual review of your firewall configuration, looking for deviations from security best practices and potential security vulnerabilities.

Office 365 Azure Security Architecture Review
Perform a security best practices review of your Azure/O365 environments with prioritized recommendations for hardening.

VPN Assessment
VPN AssessmentVPN penetration testing is a critical practice for ensuring the security of Virtual Private Networks. It involves simulating cyber attacks to identify vulnerabilities that could be exploited by malicious actors. This process helps organizations proactively address security weaknesses before they can be exploited in real-world attacks. The testing typically includes planning, port scanning, #ngerprinting, and exploiting vulnerabilities to assess the e$ectiveness of existing security controls. It is essential for compliance with data security and privacy regulations, demonstrating a commitment to robust cybersecurity practices, and building trust with clients and stakeholders
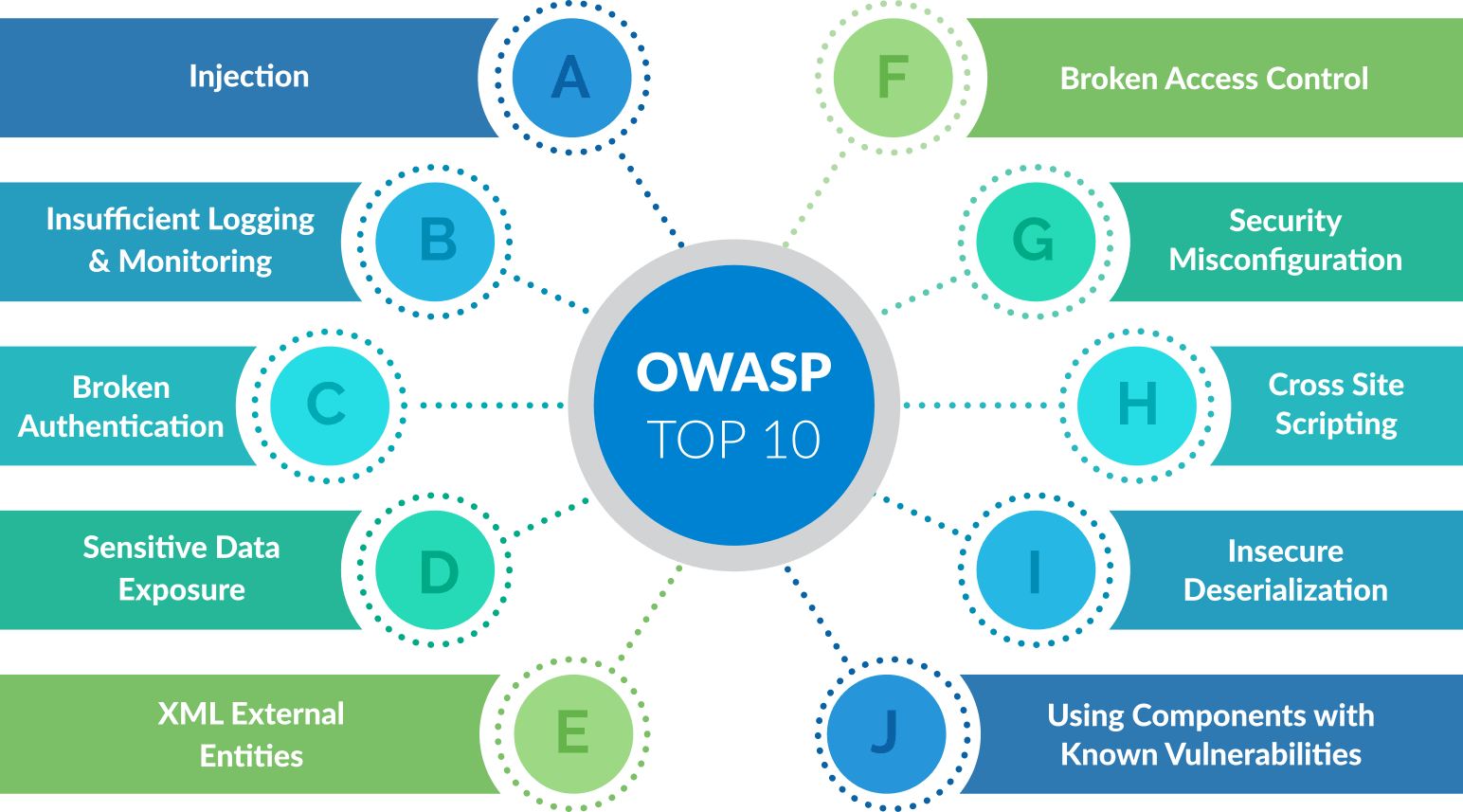
Web Application Penetration Testing (OWASP 10)
OWASP web application penetration testing is a security assessment methodology focused on identifying and validating the most critical security risks de#ned by the Open Worldwide Application Security Project (OWASP). At Pentagram Secure, our testers utilize the OWASP Top 10 as a primary framework to ensure coverage of high-impact vulnerabilities.

Active Directory Penetration Testing
Active Directory (AD) penetration testing simulates real-world attacks to #nd weaknesses in an organization's AD infrastructure, focusing on gaining unauthorized access, escalating privileges, moving laterally across the network, and ex#ltrating data by exploiting miscon#gurations, weak credentials, and vulnerabilities in user/group policies, ultimately helping secure critical identity and resource management. At Pentagram Secure, our testers use techniques like credential theft, NTLM/Kerberos relay attacks, and enumeration to uncover 4aws, mimicking attackers' steps to provide actionable remediation advice

Digital Forensics
Digital forensics, also known as digital forensic science, encompasses the recovery and investigation of material found in digital devices, often in relation to cybercrime. It has evolved from its origins in computer forensics to include all devices capable of storing digital data, such as computers, smartphones, tablets, and IoT devices. At Pentagram Secure, our forensic examiner primary goal is to preserve evidence in its original form while conducting a structured investigation, which is crucial for legal proceedings.

IoT penetration testing
IoT penetration testing is a simulated cyberattack on an Internet of Things ecosystem to find security 4aws in devices, #rmware, networks, apps, and cloud connections, aiming to identify weaknesses like weak passwords or unencrypted data before real attackers exploit them to steal data, gain unauthorized access, or disrupt services. It's crucial because IoT devices often have unique vulnerabilities, requiring testing of the entire interconnected system, not just the device. Typical vulnerabilities include:Weak Authentication: Default or weak passwords are a common 4aw.Communications Without Encryption: Information sent without encryption is vulnerable.Lack of Updates: Devices often run outdated firmware with unresolved security issues.Overlooked Design Flaws: Security is often not a priority during product development.

SCADA
¤ Protect industrial networks such as automotive, oil & gas, water, power/grid, manufacturing, and others from cyber threats, malicious insiders, and human error. ¤ Maximize visibility, security and control of your operational environments for SCADA systems, PLCs, DCS, IEDs, HMIs and more. ¤ Get all the security tools and reports for your IT and OT engineers, providing unparalleled visibility into converged IT/OT segments and ICS networks in a single window.

Websites source Code Review
A secure code review is a process where security experts analyze source or compiled code to identify potential security vulnerabilities. The goal of a secure code review is to provide an independent assessment of the security posture of software and make recommendations for improving the security posture of an application. Secure code reviews are an essential part of software security assurance and can help identify potential security vulnerabilities that could be exploited by attackers. Code reviews can also help assess the effectiveness of security controls in place, such as input validation and output encoding. When conducted properly, code reviews can be an effective way to improve the security of software.

Cloud Penetration Testing
In recent years, a number of SMEs have opted to switch to a cloud-based hosting environment, that takes the pressure off of onsite server maintenance. As a result of this shift, attackers target cloud-based servers for configuration loopholes and exposed data. A cloud configuration assessment will benefit any business that hosts its servers and databases within the cloud and would like assurance it has been configured correctly and securely. Cloud penetration testing is the process of assessing the security configuration of a cloud computing environment. The goal of cloud penetration testing is to identify vulnerabilities and weaknesses in a system that attackers could exploit. Cloud security test adheres to the guidelines set forth by the cloud service providers, such as: Amazon Web Services (AWS), Microsoft Azure, Google Cloud Platform (GCP).

IoT penetration testing
IoT penetration testing is a simulated cyberattack on an Internet of Things ecosystem to find security 4aws in devices, #rmware, networks, apps, and cloud connections, aiming to identify weaknesses like weak passwords or unencrypted data before real attackers exploit them to steal data, gain unauthorized access, or disrupt services. It's crucial because IoT devices often have unique vulnerabilities, requiring testing of the entire interconnected system, not just the device. Typical vulnerabilities include:Weak Authentication: Default or weak passwords are a common 4aw.Communications Without Encryption: Information sent without encryption is vulnerable.Lack of Updates: Devices often run outdated firmware with unresolved security issues.Overlooked Design Flaws: Security is often not a priority during product development.

SCADA
¤ Protect industrial networks such as automotive, oil & gas, water, power/grid, manufacturing, and others from cyber threats, malicious insiders, and human error. ¤ Maximize visibility, security and control of your operational environments for SCADA systems, PLCs, DCS, IEDs, HMIs and more. ¤ Get all the security tools and reports for your IT and OT engineers, providing unparalleled visibility into converged IT/OT segments and ICS networks in a single window.

Websites source Code Review
A secure code review is a process where security experts analyze source or compiled code to identify potential security vulnerabilities. The goal of a secure code review is to provide an independent assessment of the security posture of software and make recommendations for improving the security posture of an application. Secure code reviews are an essential part of software security assurance and can help identify potential security vulnerabilities that could be exploited by attackers. Code reviews can also help assess the effectiveness of security controls in place, such as input validation and output encoding. When conducted properly, code reviews can be an effective way to improve the security of software.

Cloud Penetration Testing
In recent years, a number of SMEs have opted to switch to a cloud-based hosting environment, that takes the pressure off of onsite server maintenance. As a result of this shift, attackers target cloud-based servers for configuration loopholes and exposed data. A cloud configuration assessment will benefit any business that hosts its servers and databases within the cloud and would like assurance it has been configured correctly and securely. Cloud penetration testing is the process of assessing the security configuration of a cloud computing environment. The goal of cloud penetration testing is to identify vulnerabilities and weaknesses in a system that attackers could exploit. Cloud security test adheres to the guidelines set forth by the cloud service providers, such as: Amazon Web Services (AWS), Microsoft Azure, Google Cloud Platform (GCP).
How Our Penetration Testing Services Work
Our assessors come equipped with the latest technologies and techniques.
We send an onsite device or an agent for network tests or request access to the application.

We use MITRE’s ATT&CK framework and OWASP top 10 to simulate typical attacks.

A certified offensive security expert provides immediate and actionable results.
We deliver the report and schedule a review call with your team and the assessor.
Penetration Testing Services Phases
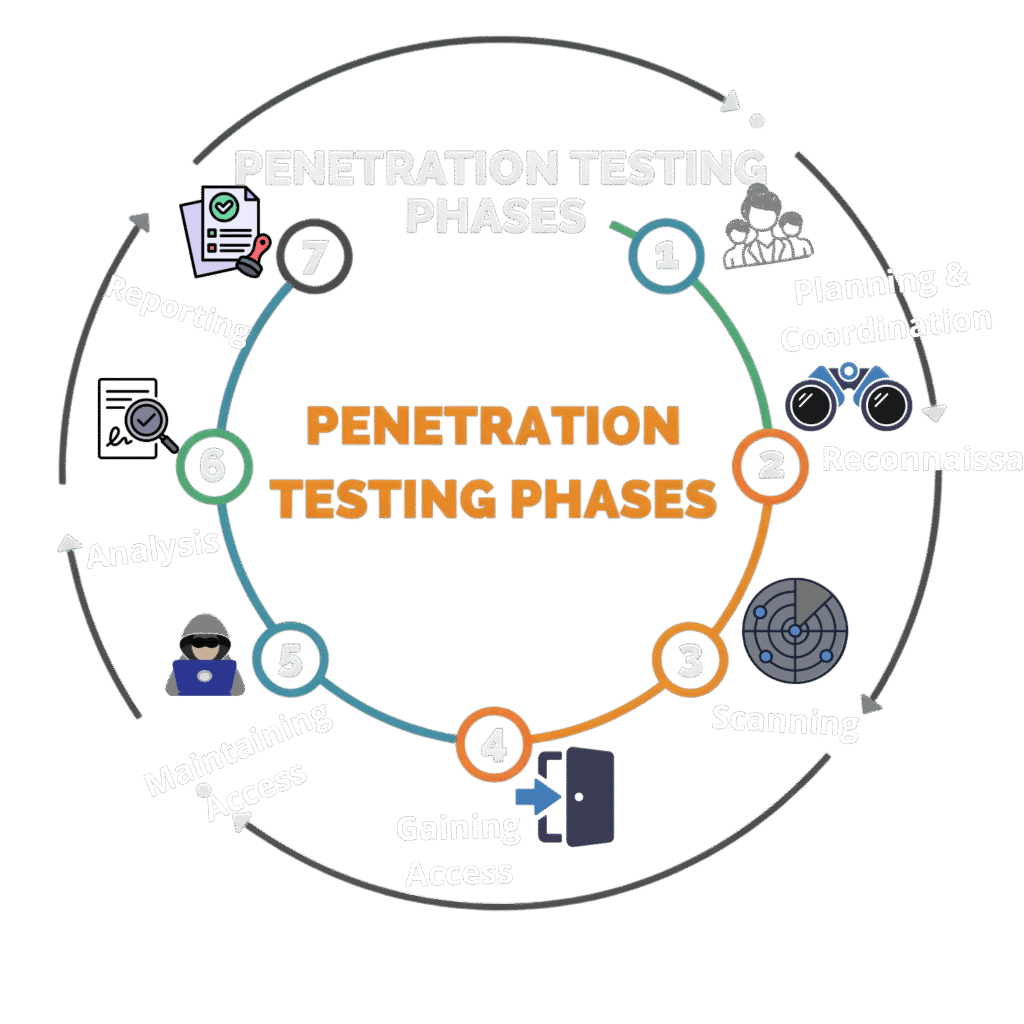

1 Planning
The first stage involves defining the scope and goals of a test, including the systems to be addressed and the testing methods to be used. Our testing team works in conjunction with engineering teams, system owners, and the client’s security team to establish the scope of our test.
2 Reconnaissance
The next step is the gathering of intelligence (e.g., network and domain names, mail server) to better understand how a target works and its potential vulnerabilities. While we hope asset inventory is 100% accurate, we know that this is rarely the case. This will involve NMAP scans and OSINT to recon and locate assets not supplied in the discovery call request.
3 Scanning
The next step is to understand how the target will respond to various intrusion attempts. This step can involve automated, manual, and security functionality testing depending on the scope of the assessment. In general, automated scans will be performed first as results from these can help expose areas that need more manual testing.
4 Gaining Access
PentagramSecure will review the identified vulnerabilities and misconfigurations. This validation is performed through targeted penetration testing that focuses on high-risk findings. Exploitation of these findings often yields access to critical systems and sensitive information vital to operations.
5 Maintaining Access
The goal of this stage is to see if the vulnerability can be used to achieve a persistent presence in the exploited system— long enough for a bad actor to gain in-depth access. The idea is to imitate advanced persistent threats, which often remain in a system for months to steal an organization’s most sensitive data.
6 Analysis
The analysis phase is where all findings will be analyzed for validity and will be assigned a risk rating. The risk rating will be assigned based on a few factors such as the ease of the exploit, what kind of asset it is attributed too, and the potential outcome if exploited.

7 Reporting
The final step has Pentagramsecure combining all findings into a report that can be understood by both technical and non-technical personnel. This report will be extremely detailed with step-by-step details on how to recreate all the major findings and recommendations on how to remediate them.
Certified Professionals